📝Abstract
LLM-driven AI agents are rapidly evolving from isolated systems into interconnected, communicating entities that collaborate with users, other agents, and external tools. Many organizations have recently proposed new communication protocols (e.g., Anthropic's MCP and Google's A2A), accelerating this transformation.
However, these emerging communication pathways introduce novel and severe security hazards, including semantic manipulation, protocol exploitation, cross-agent misinformation cascades, and unsafe delegation — risks that go beyond traditional single-LLM vulnerabilities.
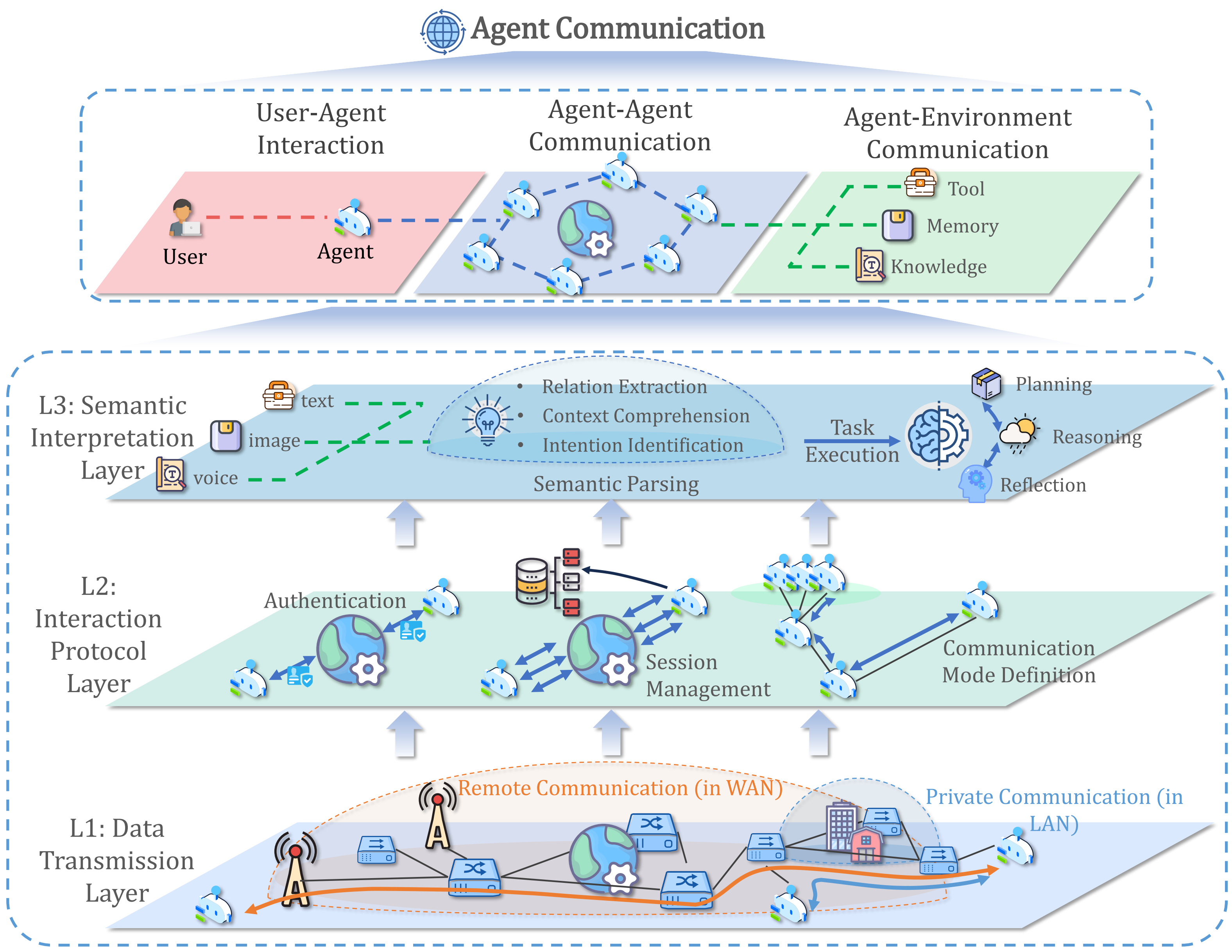
To address this, our paper presents the first comprehensive survey of agent communication security. We unify the definition of agent communication, introduce a 3-class × 3-layer architecture, analyze representative protocols, security risks and propose structured defense methodologies, conduct empirical studies on MCP and A2A, and outline open challenges for future research.
🧩Communication–Layer Matrix
We model agent communication across three classes and three security-relevant layers:
| Layers ↓ / Classes → | User ↔ Agent | Agent ↔ Agent | Agent ↔ Environment |
|---|---|---|---|
| 🔵 L1 — Data Transmission | ⚠️Risks 🛡️Defenses | ⚠️Risks 🛡️Defenses | ⚠️Risks 🛡️Defenses |
| 🟣 L2 — Interaction Protocols | 📡Protocols ⚠️Risks 🛡️Defenses |
📡Protocols ⚠️Risks 🛡️Defenses |
📡Protocols ⚠️Risks 🛡️Defenses |
| 🔶 L3 — Semantic Interpretation | ⚠️Risks 🛡️Defenses | ⚠️Risks 🛡️Defenses | ⚠️Risks 🛡️Defenses |
Each cell corresponds to detailed collections of protocols, risks, and defenses curated in the GitHub repository.
🌟Highlights
- 🧭 Clear Conceptualization: Provides the first precise and unified definition of agent communication, consolidating fragmented views in the literature.
- 🏗 Systematic Taxonomy: Proposes a three-class, three-layer framework that rigorously maps communication processes to their corresponding security risks.
- ⚠️ Risk Analysis: Dissects representative protocols (e.g., MCP, A2A, CS-based and P2P-based schemes) and locates risks at L1 (Data Transmission), L2 (Interaction Protocol), and L3 (Semantic Interpretation).
- 🛡️ Defensive Outlook: Summarizes defense methodologies including content filtering, multi-agent consensus, architectural isolation, trusted routing, and semantic integrity verification.
- 🔍 Empirical Demonstration: Conducts experiments on real-world communication frameworks (MCP and A2A), revealing novel vulnerabilities in practical agent systems.
- 🚀 Future Directions: Highlights open challenges such as multi-agent hallucination cascades, security-aware protocol co-design, and formal guarantees for semantic integrity in agent communication.
📦Code & Resources
This work is accompanied by an actively maintained, curated repository:
GitHub: https://github.com/theshi-1128/awesome-agent-communication-security
The repository includes:
- 🧩 Categorized collections of communication protocols (user–agent, agent–agent, agent–environment)
- ⚠️ Detailed risk taxonomies and attack examples across L1–L3
- 🛡️ Defense strategies and architectural patterns
- 🧪 Experiment setups and notes for MCP and A2A
- 📚 An evolving list of related papers and reports
We plan to keep tracking the latest protocols, security analyses, and defense techniques to support reproducible research and foster future work on secure agent communication.
📖Citation
If you find this work useful in your research, please consider starring the repository ⭐ and citing:
@article{kong2025survey,
title={A survey of llm-driven ai agent communication: Protocols, security risks, and defense countermeasures},
author={Kong, Dezhang and Lin, Shi and Xu, Zhenhua and Wang, Zhebo and Li, Minghao and Li, Yufeng and Zhang, Yilun and Peng, Hujin and Sha, Zeyang and Li, Yuyuan and others},
journal={arXiv preprint arXiv:2506.19676},
year={2025}
}You can also find the latest version of the paper on arXiv:2506.19676.
🤝Contact & Contributions
We welcome contributions, feedback, and collaboration opportunities!
💬 Issues & PRs: GitHub Issues
📧 Email: linshizjsu@gmail.com, kdz@zju.edu.cn


